The Session Initiation Protocol (SIP) is a signaling protocol used for initiating, managing, and terminating real-time communication sessions over the Internet.
SIP works in conjunction with other protocols like RTP, SDP, etc to facilitate audio/video calls, instant messaging, presence information, etc.
A core component of any SIP network is the SIP proxy server. It plays a crucial role in routing SIP messages and enabling connectivity between users across domains.
This article provides an in-depth look at SIP proxy servers – their working, types, features, and benefits.
It also answers some frequently asked questions to help gain a well-rounded understanding of this fundamental building block powering modern IP communications.
Key Functions of a SIP Proxy Server
- Routing of SIP messages: A proxy server determines the next hop for forwarding requests based on configured rules and policies. This enables connectivity between users within and across SIP domains.
- Network policy enforcement: Proxy servers can enforce policies defined by the network administrator e.g. call admission control, firewall transversal, codec restriction, etc.
- Security: Proxies can perform authentication and prevent unauthorized usage of SIP services.
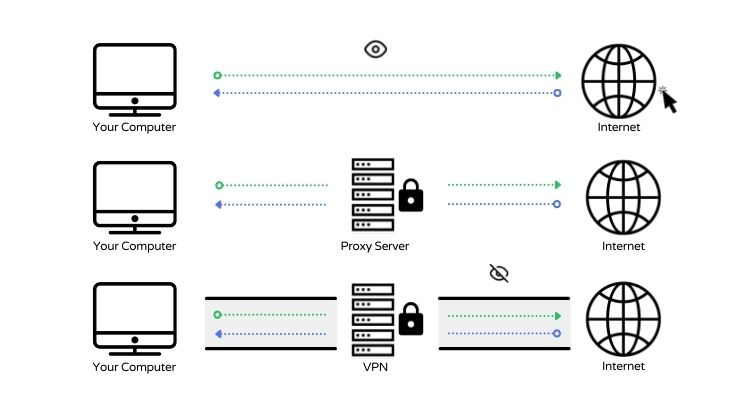
- Load balancing: Proxies distribute network load across servers and improve scalability.
- NAT traversal: Proxies facilitate communication across NAT firewalls using techniques like STUN, TURN, etc.
Types of SIP Proxy Servers
There are two main types of proxy servers:
1. Stateful Proxy
- Maintains session state and dialog information for the duration of a call.
- Can perform advanced session control functions.
- Offer more flexibility but are relatively complex and resource-intensive.
2. Stateless Proxy
- Forwards requests without keeping track of dialog state.
- Faster and more scalable but offers limited functionality.
- Cannot handle advanced session control mechanisms.

Features of using a proxy server
Some key features offered by SIP proxy servers:
- Protocol compliance – Support SIP and related protocols for multimedia signaling.
- Authentication and security – Apply access control, encrypt transactions, and prevent attacks.
- Routing and load balancing – Route each request to the appropriate destination based on policies. Distribute load effectively.
- Protocol normalization – Resolve protocol differences between endpoints.
- NAT traversal – Facilitate communication across NAT boundaries.
- Codec management – Restrict codecs to control bandwidth usage.
- Accounting and billing – Measure usage for billing purposes.
Benefits of using a proxy server
- Reduced administrative overhead compared to managing user agents directly.
- Flexible call routing and number portability.
- Robust security and network policy enforcement.
- Scalability through load balancing.
- Normalization – resolves endpoint capability differences.
SIP Proxy Server Architecture
The typical architecture of a SIP proxy server consists of:
1. SIP Protocol Stack
Implements SIP (RFC 3261) and related protocols like SDP, RTP/RTCP, etc. It manages SIP messaging, sessions, and negotiations with endpoints.
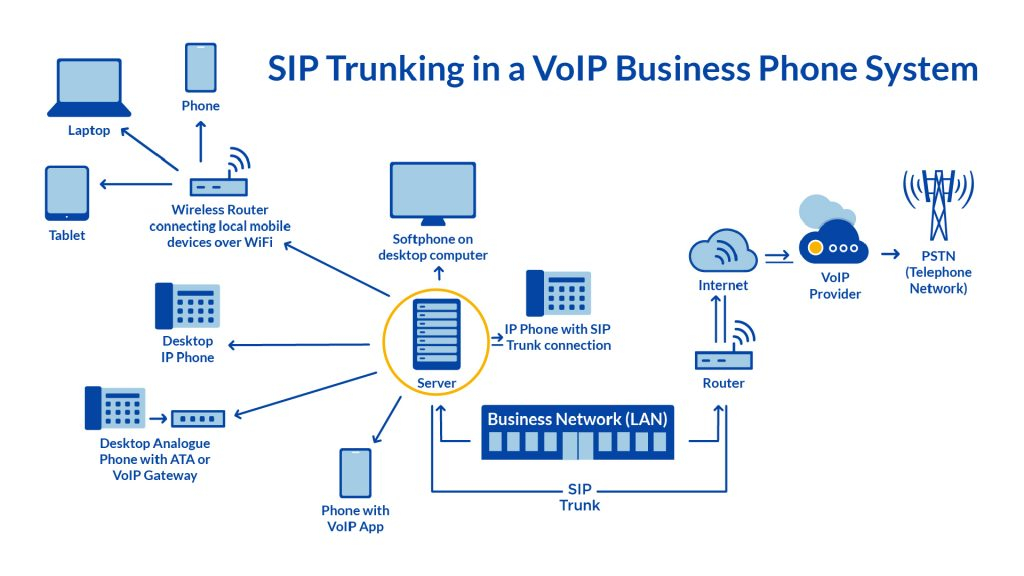
2. Network Interfaces
Provide physical connectivity to the SIP network over LAN, WAN, or internet. This includes Ethernet, T1/E1, etc.
3. Routing Engine
Makes routing decisions to direct incoming SIP messages to the appropriate destination based on configured proxy rules and policies.
4. Policy Control
Applies policies defined by the network admin for security, session control, QoS monitoring, etc.
5. NAT Traversal
Enables connectivity across NAT devices using STUN, TURN, or other methods.
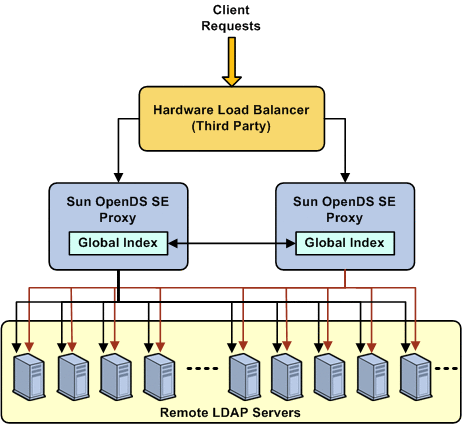
6. Load Balancer
Distributes requests and network load across multiple proxy node machines for better scalability.
7. AAA Server Interface
Interfaces with external AAA servers for authenticating and authorizing SIP clients.
8. Server Clustering
Allows pooling multiple proxy server nodes to appear as a single logical entity, providing redundancy and higher capacity.
9. Management Interface
Allows the server configuration and policies to be monitored and managed remotely by the administrator.
SIP Proxy Server Message Flow
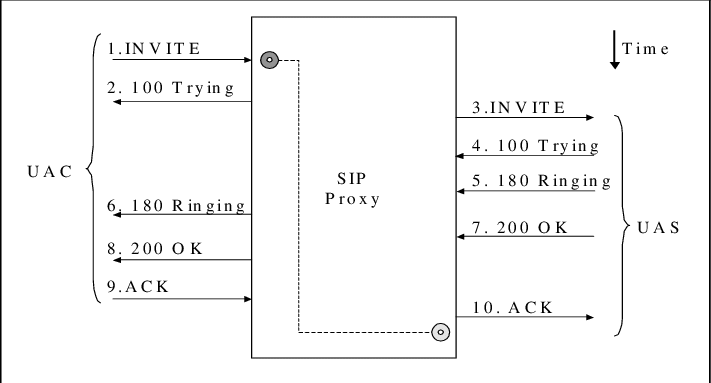
The basic SIP message flow through a proxy server is:
- A SIP user agent sends a request message like INVITE or REGISTER to the proxy server.
- The proxy processes the message. It may authenticate the user, apply security policies, load balancing, etc.
- The proxy determines the next hop for the request based on configured proxy routing rules and policies.
- The request is forwarded to the next destination, which could be another proxy server or the destination UA.
- The response generated comes back through the proxy to the source UA.
- The proxy server forwards the response back to the originating UA after processing.
During an active session, the proxy keeps forwarding requests and responses between the participating UAs or endpoints.
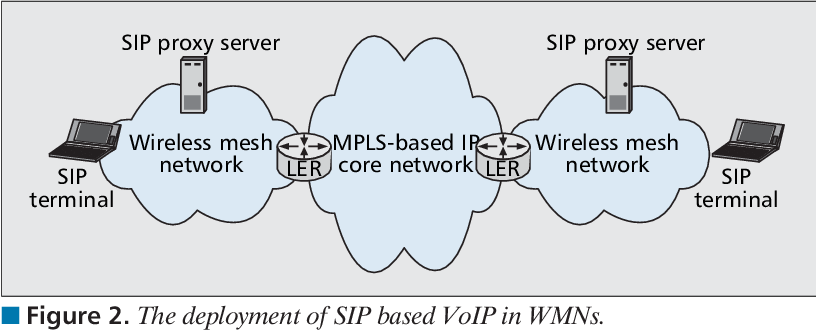
SIP Proxy Server Deployment Models
SIP proxy servers can be deployed in different network architectures:
1. Single Proxy
A single proxy server caters to all users in a domain. It maintains registrations and handles all session requests.
2. Multiple Proxies
Multiple proxy servers can share the load for large networks. This provides redundancy and ensures there is no single point of failure.
3. Proxy Hierarchy
Proxies can be arranged hierarchically in a tree-like structure for large service provider networks. Requests are routed up and down the hierarchy.
4. Proxy Mesh
Proxies communicate with each other in a mesh topology, providing multipath connectivity between SIP nodes. If one link fails, requests can be rerouted through alternate proxies.
The appropriate deployment model depends on the scale, high availability requirements, and topology of the SIP network.
Large distributed environments often use a combination of the above architectural patterns.
Best Practices for SIP Proxy Design
Some best practices for designing robust and scalable SIP proxy server deployments:
- Horizontally scalable – Allow linear capacity increase by adding more proxy nodes.
- Redundant proxies – Eliminate single points of failure using standby backup proxy servers.
- Load balancing – Distribute load intelligently across proxy clusters using round robin or least loaded algorithm.
- Priority routing – Route high-priority or emergency calls through dedicated proxy nodes.
- Geo-redundant proxies – Place proxies in multiple geographic regions for disaster recovery.
- Virtualization – Run proxies on VMs with orchestration for elastic scale out.
- Tune network buffers – Adjust TCP buffer sizes, and socket concurrency for optimal performance.
- Monitor QoS – Track metrics like latency, jitter, and packet loss to maintain voice quality.
- Media anchoring – Anchor media streams to avoid transcoding and save resources.
- Secure access – Enforce strong password policies, IP whitelisting, TLS encryption, etc.
SIP Proxy Server Manufacturers
Some leading vendors providing SIP proxy server platforms and solutions:
- Cisco – Cisco Unified Communications Manager, Cisco Unified Border Element
- Avaya – Avaya Aura Session Manager
- Oracle – Oracle Session Border Controller
- Ribbon – Ribbon SBC Software Edition
- AudioCodes – AudioCodes Mediant Session Border Controller
- Grandstream – Grandstream UCM series IP PBX
- Mitel – Mitel MiVoice Border Gateway
- Sangoma – Sangoma SBCs
- Metaswitch – Metaswitch Perimeta SBC
- Sonus – Sonus (Ribbon) SBC 5000 Series
Frequently Asked Questions (FAQ)
Ques 1. What is the main difference between an SIP proxy and an SIP user agent?
Ans. A SIP user agent (UA) represents an endpoint device like an IP phone, SIP phone, or softphone client.
It initiates and terminates SIP calls. A SIP proxy server acts as an intermediary that receives requests from UAs or other proxies and forwards them to the next hop.
Ques 2. How does a SIP proxy server scale to handle large numbers of users?
Ans. SIP proxy servers can scale using clustering and load balancing across multiple proxy nodes.
This allows linear capacity to increase as more proxy servers are added. Geographic redundancy also improves scalability.
Ques 3. What security mechanisms do SIP proxy servers implement?
Ans. SIP proxies support security measures like TLS encryption, mutual authentication using SIP over TLS, IP address whitelisting, digest authentication of user credentials, encryption of sensitive headers, etc.
Ques 4. Which protocol helps SIP traverse NAT firewalls?
Ans. SIP proxies use protocols like STUN, TURN, and ICE to discover public IP addresses and ports and negotiate connections across NAT devices.
This enables SIP calls between users behind NAT firewalls.
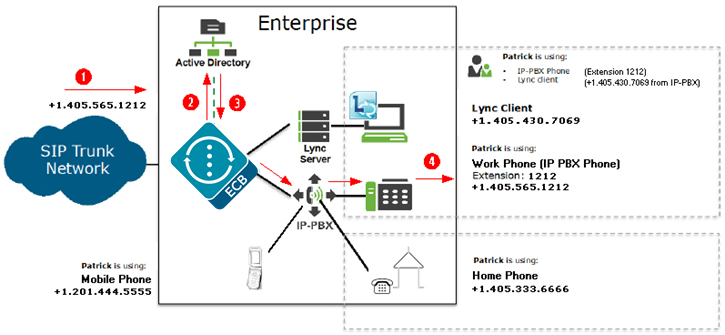
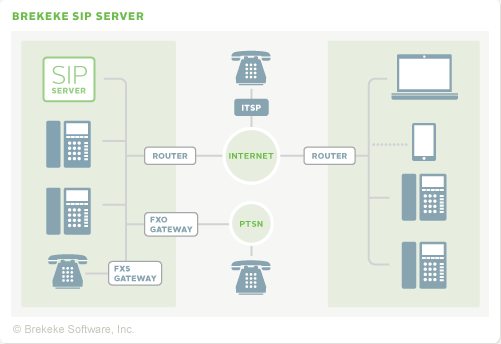
Ques 5. Can SIP proxy servers mediate calls between IP-based and PSTN networks?
Ans. Yes, SIP proxy servers like session border controllers can interface between IP-based SIP networks and PSTN or cellular networks.
They perform protocol conversion between SIP and PSTN signaling like ISUP or BICC.